California scientists ‘FlyTrap attack’ on DJI drones demonstrated — patterned umbrellas lure autonomous drones close enough to be captured or even induced to crash
- Innovative use of patterned umbrellas exploits vulnerabilities in drone autonomous tracking systems.
- The FlyTrap attack demonstrates a low-cost, portable method to capture or disable DJI drones.
- Research highlights risks in autonomous drone navigation and implications for drone security.
- Potential applications in drone defense, privacy protection, and counter-surveillance strategies.
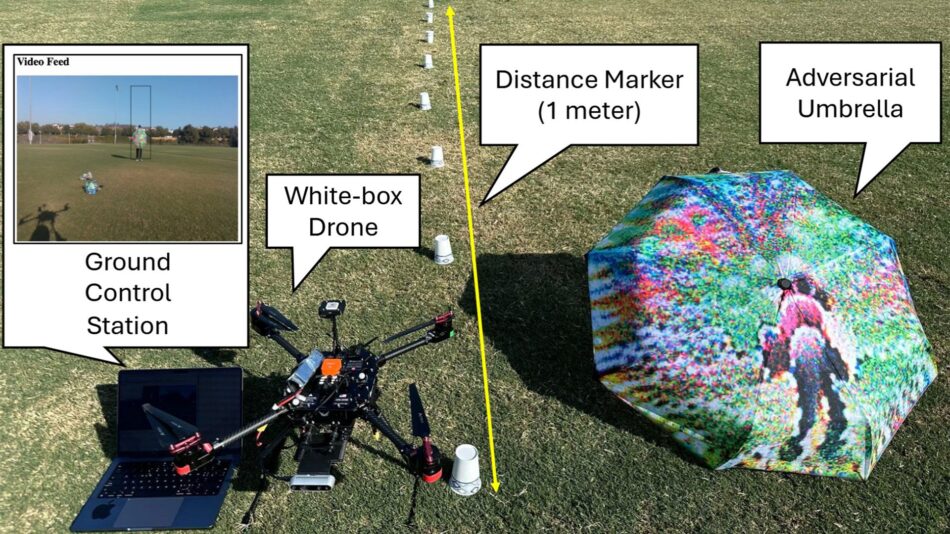
Researchers at the University of California, Irvine have unveiled a novel technique called the FlyTrap attack that leverages specially designed patterned umbrellas to manipulate and capture DJI drones. This method exploits inherent weaknesses in the drones’ autonomous target tracking technology, commonly known as Active Track or Motion Track. By presenting visually disruptive patterns, the umbrellas lure drones close enough to be physically captured or even forced to crash, revealing critical vulnerabilities in current drone systems.
This discovery not only raises concerns about the security of autonomous drone operations but also opens new avenues for drone defense mechanisms. The FlyTrap device is portable, inexpensive, and effective against popular commercial drones, making it a significant breakthrough in the field of drone countermeasures and cyber-physical security. Understanding this attack can help businesses and governments develop better strategies to protect sensitive airspace and privacy.
Continue Reading
What is the FlyTrap Attack and How Does It Work?
The FlyTrap attack is a physical adversarial technique designed to exploit the visual processing algorithms of DJI drones, which rely heavily on camera-based autonomous tracking. The attack uses a patterned umbrella featuring high-contrast, repetitive designs that confuse the drone’s onboard computer vision systems. When a drone attempts to lock onto a target using its Active Track feature, the umbrella’s patterns disrupt the tracking algorithm, causing the drone to misinterpret the visual input.
As a result, the drone is lured closer to the umbrella, mistaking it for a valid target or losing track of its intended subject. This proximity allows an operator or automated system to capture the drone physically or induce a crash by forcing erratic flight behavior. The FlyTrap attack leverages weaknesses in the drone’s machine learning models that govern object recognition and motion prediction.
Key Components of the FlyTrap Attack
- Patterned visual stimuli: The umbrella’s design is carefully crafted to exploit the drone’s visual tracking algorithms.
- Portability: The umbrella is lightweight and easy to deploy in various environments.
- Exploitation of ATT systems: Targets the Active Track and similar autonomous tracking technologies used by DJI drones.
- Physical capture or crash induction: Enables safe drone neutralization without electronic jamming or hacking.
Why Are DJI Drones Vulnerable to the FlyTrap Attack?
DJI drones dominate the commercial drone market and are equipped with sophisticated autonomous flight capabilities, including Active Track, which allows drones to follow subjects without manual control. These features rely on deep learning-based object detection and tracking systems that process visual data in real time.
However, these algorithms are susceptible to adversarial inputs—visual patterns that cause the AI to misclassify or lose track of objects. The FlyTrap attack exploits this by presenting a visual stimulus that confuses the drone’s perception, causing it to behave unpredictably. The research from UC Irvine demonstrates that even commercially available drones, with their advanced AI, can be manipulated by relatively simple physical objects.
Technical Vulnerabilities Exploited
- Camera-based tracking limitations: The drones depend heavily on visual cues, which can be spoofed.
- Algorithmic blind spots: The AI models do not robustly handle certain pattern disruptions.
- Insufficient sensor fusion: Limited integration of other sensors like radar or lidar reduces redundancy.
Implications for Drone Security and Privacy
The FlyTrap attack highlights significant concerns for drone cybersecurity and privacy. As drones become more autonomous and prevalent in commercial, recreational, and governmental use, their susceptibility to physical adversarial attacks poses risks such as unauthorized capture, data theft, or forced crashes leading to property damage or injury.
Organizations relying on drones for surveillance, delivery, or inspection must consider these vulnerabilities in their risk assessments. The FlyTrap method also offers a non-invasive countermeasure option for individuals or entities seeking to protect their privacy from unwanted drone surveillance without resorting to electronic jamming, which may be illegal or disruptive.
Potential Use Cases for FlyTrap Technology
- Drone interdiction by law enforcement or security agencies.
- Privacy defense for private citizens against intrusive drone monitoring.
- Protection of sensitive sites such as government buildings or critical infrastructure.
- Research and development of improved adversarial AI defenses in autonomous systems.
How Can Drone Manufacturers Mitigate These Vulnerabilities?
To defend against attacks like FlyTrap, drone manufacturers need to enhance the robustness of their autonomous tracking algorithms. This includes improving the AI’s ability to recognize and ignore adversarial patterns and integrating multiple sensor modalities to cross-verify target tracking.
Some mitigation strategies include:
- Multi-sensor fusion: Combining camera data with radar, lidar, or ultrasonic sensors to reduce reliance on visual input alone.
- Adversarial training: Incorporating adversarial examples into the AI training process to improve resilience.
- Algorithmic improvements: Developing more sophisticated object recognition models that can detect spoofing attempts.
- Fail-safe mechanisms: Programming drones to disengage or return to home if tracking anomalies are detected.
Cost, Scalability, and Risks of the FlyTrap Attack
The FlyTrap attack is cost-effective and scalable due to its reliance on simple physical props rather than expensive electronic countermeasures. An umbrella with a printed pattern costs little and can be easily carried by security personnel or civilians. This low barrier to entry makes the attack accessible and potentially widespread.
However, risks include legal and ethical considerations. Using FlyTrap to capture or disable drones may violate local laws or regulations, especially if it causes damage or endangers people. Additionally, malicious actors could misuse the technique to disrupt legitimate drone operations, such as emergency response or commercial deliveries.
Future Research and Development Directions
The FlyTrap research opens new avenues for exploring physical adversarial attacks on autonomous systems beyond drones. Future studies may focus on:
- Developing standardized tests for AI robustness against physical adversarial inputs.
- Designing counter-adversarial technologies that detect and neutralize pattern-based attacks in real time.
- Exploring applications in other autonomous vehicles, such as self-driving cars or robots.
- Enhancing legal frameworks to address emerging drone security challenges.
Summary
The FlyTrap attack by UC Irvine scientists reveals a novel, practical vulnerability in DJI drones’ autonomous tracking systems. By using patterned umbrellas, attackers can lure drones close enough to capture or crash them, exploiting weaknesses in AI-driven autonomous navigation. This discovery underscores the urgent need for improved drone cybersecurity measures and offers a new perspective on physical adversarial attacks in the evolving landscape of autonomous drone technology.
Frequently Asked Questions
Call To Action
Protect your drone operations by understanding vulnerabilities like the FlyTrap attack and investing in advanced AI security solutions to ensure safe and reliable autonomous flight.
Note: Provide a strategic conclusion reinforcing long-term business impact and keyword relevance.